The cloud has become an extremely popular place for developers to place IoT systems and devices. The strengths of the cloud lie in how easy it is to scale up and how straightforward it is for users. That being said, that doesn’t tell the whole story.
As the Internet of Things (IoT) continues to grow, the concern around IoT cloud security is also heightening.
In this guide, we will lay out some of the best practices for IoT and cloud security. That way, you can keep yourself and your users safe whether they’re on the cloud or an alternative data storage location.
Why is IoT Cloud Security Such a Concern?
The world of IoT is becoming larger than ever before. It’s no longer occupied solely by businesses and hobbyists. The emergence of home automation devices – such as Google Nest – and other smart devices means IoT and the cloud now have entered the mainstream.
While this makes everyone’s lives a lot easier, it also provides hackers with a larger group to target. We’ve had a couple of decades to get clued up with how to stay safe on the internet. However, IoT has not been around long enough for the public to be clued up on the various security challenges posed by using the cloud with IoT devices.
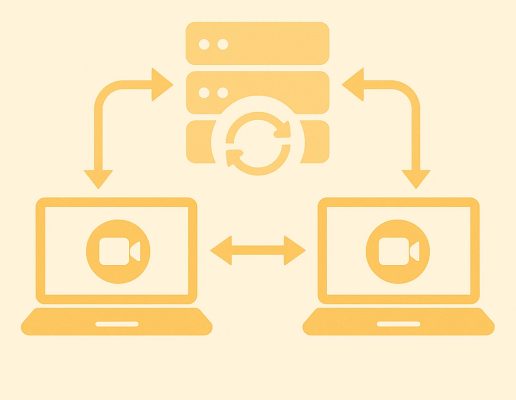
Herein lies the biggest issue. Users are transmitting data back and forth to a centralized server within the cloud with little idea of how to protect that data. In the world of IoT, it doesn’t just affect them – it affects everyone they interact with.
So, to save people from themselves, you need to make sure you’re prioritizing cloud and IoT security.
If you want some more tips on IoT security and privacy, check out our guide on overcoming IoT security and privacy challenges.
The 5 Best Practices For Ensuring IoT Cloud Security
Regularly Update Passwords For Devices Used On the Cloud
Hackers can get access to intelligent devices if passwords are stored on the cloud. And while a lot of people know the importance of changing passwords once a security breach has been flagged, it’s a good idea to act instead of react.
Therefore, we recommend you encourage users to change their passwords frequently. This could prevent security problems and issues down the line.
The best option is to not only use a secure password but to do this in combination with an extra line of defense, normally described as two-factor authentication. This is typically done by combining the password with a token like a one-time code transmitted via a secondary, secure line (smartphone text message) or a beforehand synchronized token generation tool.
Take the High Road With Secure Software Development
At the moment of writing, there are still no universal standards and practices that IoT manufacturers have to abide by when it comes to new IoT devices.
As a result, security can be overlooked – especially those who manufacture smaller devices, where they have to be stringent on the amount of code added. However, this approach is risky. All it takes is one significant security breach, and your customers and consumer trust plummet.
Therefore, you should take the high road and make your hardware as secure as you can. One way to do so is by implementing encrypted storage. On top of that, if you’re an IoT developer, you should be considering software security throughout the life cycle of your device.
Carry Out Regular Checks and Maintenance On Your System
If you’re using a centralized cloud system, you’ll need operators on hand to carry out regular checks and maintenance. This will both tackle any security breaches as soon as possible and ensure that your IoT infrastructure is working properly. This can be a slightly frustrating and unpredictable use of your resources, but it’s necessary.
On top of this, you’ll also need to ensure that your antivirus and malware software is up to date.
BONUS TIP: Don’t forget about physical security! Protecting USB ports and other physical access points is also important. Some of the worst security attacks against cloud-based IoT infrastructures are made via physically accessing devices.
Keep Authentication Keys Safe
This step is kind of jumping ahead and assuming you’ve already put IoT encryption algorithms and keys in place. So, if you haven’t, make sure you do just that.
After that, you want to include an authentication key – or another IoT device authentication method – in order to identify them when accessing data stored in the cloud. Moreover, to keep them safe, make sure one or several copies of these authentication keys are stored in a secure location.
Stay Up to Date with Code or App Security Best Practices
Both code and applications play an integral role in securing IoT cloud ecosystems. When used well, they can provide you with simplified control and usability of your IoT solution.
So, while it’s also a good idea to keep up to date with the latest cybersecurity news and threats to be wary of, it’s also worth keeping abreast of the best code or app practices you can use. IoT forums, websites well respected within your industry, and expert IoT blogs should become regular reading.
Bonus Tip: Skip the Cloud Altogether With a Decentralized IoT Platform
If you’re overly concerned with cloud and IoT security, then the only way to completely remove these concerns is to skip the cloud and use a decentralized IoT Application Enablement Platform (AEP).
Most “traditional” AEP solutions (such as AWS IoT or Microsoft Azure) store data centrally in the cloud. The issue here is the inherent vulnerability of data in centrally stored databases.
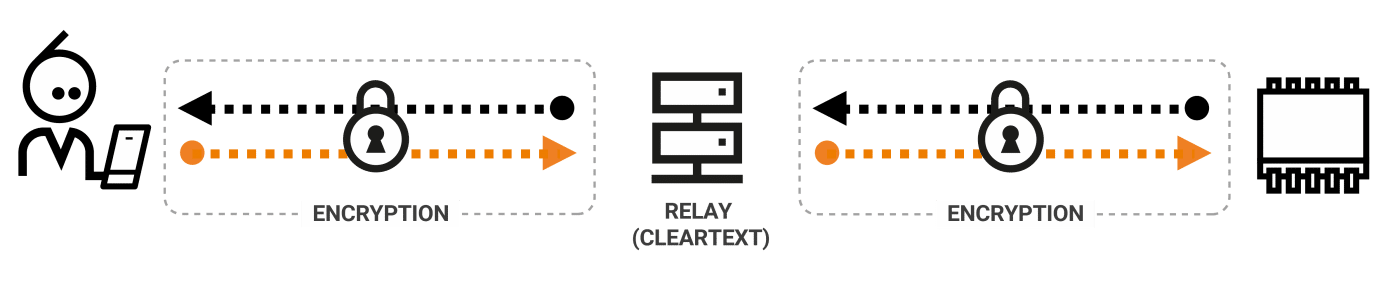
However, in a decentralized AEP, such as a P2P platform, data flows directly between the client and the IoT device, and all data is stored securely in the IoT device rather than the cloud.
This allows the user to have complete control over the data residing on their network, and, therefore, the risk of a third party intercepting data is almost eradicated.

Here at Nabto, our IoT Application Enablement Platform uses peer-to-peer connectivity to decentralize data processing and storage, removing many of the security vulnerabilities of traditional cloud-based AEPs.
Find out more about how Nabto’s IoT platform can offer your user’s more robust privacy and security here.
The Bottom Line
As the world of IoT and the cloud continue to be a mystery to the average user, you need to ensure you’re taking all the steps you can to protect your users. The alternative? You suffer a security breach and lose both customers and trust in your product.
As you can see from the tips, a lot of the tips are staying up to date with the latest threats out there, how your system is performing, and regularly updating passwords and keys. Therefore, it’s not difficult to do. Don’t keep your head in the clouds! Follow these simple best practices, and you’ll conquer IoT and cloud security once and for all.
If you want to learn more about Nabto’s IoT Solutions – or simply want to hear what we recommend for your IoT device – get in touch with us today.
Read Our Other Resources
We’ve published a range of IoT resources for our community, including:
- How to Overcome IoT Security & Privacy Challenges, which provides an overview of keeping your customers’ data safe and private in the world of IoT.
- Buying versus building an IoT platform, which discusses how to choose the best option for you.
- Our guide on how to Develop IoT Apps and what platforms you can use.
- A Comparison of IoT Protocols for Developers will help you find the perfect protocol for your device
- Find the right microcontroller by reading our Complete Guide to Microcontrollers for IoT.