In this connected world, you would naturally expect to be able to view video surveillance remotely from your computer or a smartphone. Thanks to the Internet of Things (IoT), you can do that. But in a majority of IoT surveillance systems, it takes a lot of effort to set up the remote communication between a camera and a receiving device.
Now you can use a peer-to-peer (P2P) system to directly connect devices like computers and smartphones with your security cameras. Let’s take a look at how to use P2P video streaming for your surveillance cameras.
The Basics of P2P Video Streaming
Understanding P2P video streaming starts with understanding the nature of a ‘“peer.” In an IoT network, peers are simply different smart devices in the network or the user devices they communicate with. A P2P system connects an end user device—like a smartphone or computer—directly to an IoT device. In the case of video streaming, the IoT device could be a surveillance camera. These are also called embedded devices, because they need a certain amount of computing power and software embedded in them in order to function and to transfer information, like a real-time video feed.
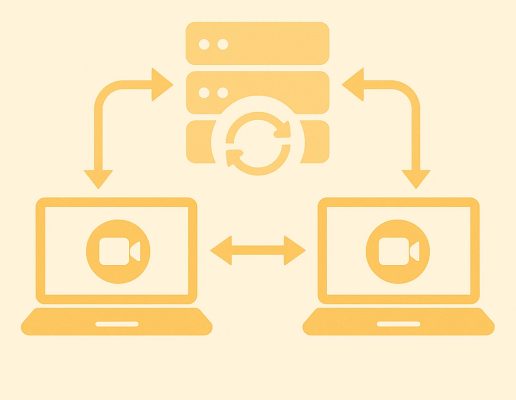
A P2P system is essentially the opposite of a client-server model, in which there is an intermediary or relay in between the peers, acting as a conduit for the communication. In most cases, the relay or intermediary would be a cloud server. Unfortunately, this client-server model can create delays in your video feed, as the communication needs to pass through several potentially busy servers before it gets to you.
So, there are plenty of benefits to bypassing third-party cloud servers. First of all, there’s less latency, or delay, in the video feed. Maybe your security cameras are supposed to start recording whenever a motion sensor detects an intruder. Latency creates a delay between the time your system detects an intruder and the recording starts and the system notifies you. When you’re talking about a potentially dangerous intruder, those seconds can be crucial. P2P reduces this latency or gets rid of it all together.

Another benefit of P2P is that you don’t have to pay the expense for a cloud server, which can be significant if your IoT network contains a multitude of devices. Also, a P2P connection tends to be more secure, since hackers can intercept your feed if it goes through the cloud. So it’s no wonder many security systems use P2P.
But there are circumstances when P2P communication can be hard to establish, such as when there are firewalls protecting both the end user device and the IoT device. In this case, any communication has to be able to get through two firewalls, preferably without a lot of hassle and extra work on your part. At the same time, the firewalls need to be able to maintain a secure system and prevent unauthorized access. So how can P2P communication rise to the challenge and solve these issues?
P2P can work in different ways. In the case of Nabto’s P2P connectivity platform, a Nabto software development kit (SDK) provides all the tools you need to easily set up P2P communication through a Transmission Control Protocol (TCP) tunnel.
TCP is simply a protocol that allows devices to recognize IP addresses and communicate with the different addresses. It’s like a kiosk at a post office that provides you with an address label for your package so it arrives at the correct physical address. A TCP tunnel is just what it sounds like. It uses the TCP protocol to create a tunnel through firewalls and provide secure remote access from user devices to IoT devices.
Configuring P2P Surveillance Systems
Nabto does the heavy lifting for you when you’re configuring a P2P surveillance system. You can add P2P communication to your existing IoT surveillance system and have it up and running within an hour. Still, it’s good to know a few more things about how security and access management work in such a system.
P2P communication is fully encrypted. Because there’s no need to decrypt the feed in a central server or database, the data remains encrypted from start to finish. That prevents unauthorized users from viewing your feed. And you can use Nabto’s Identity and Access Management (IAM) features to define what an authorized user looks like across all your devices. You can also pair specific IoT devices with specific user devices, assign different roles to users, and limit admin permissions.
What’s more, Nabto provides P2P connectivity to as many devices as you need. If you’re using a client-server model for a large network of security cameras, not only do the cloud servers become expensive, but they also get overloaded. Because the Nabto platform bypasses those servers, the load is lightened and even a large number of cameras can easily connect and communicate with user devices in real time.
If you want to learn more about the specifics of bringing P2P video streaming to your surveillance system, request a consultation with one of our IoT experts. While P2P communication used to be complex and difficult to set up and use, it’s now easier and faster than ever.
Read Our Other Resources
We’ve also published a range of IoT resources for our community, including:
- Read a full explanation of P2P technology https://www.nabto.com/p2p-explainer/
- Learn about the benefits of P2P for smart security devices https://www.nabto.com/benefits-p2p-iot-technology-smart-security-devices/
- Discover why the cloud isn’t always the best option for IoT https://www.nabto.com/iot-and-the-cloud-problems/
- Read more about video streaming with Nabto