In recent months both Amazon and Microsoft have launched new IoT solutions to create more secure tunneling between the end-user and the IoT device. The two solutions, the AWS IoT Device Management and the Azure IoT Device Stream have a lot in common, but compared to the Nabto IoT platform they still lack some important features when it comes to performance and user privacy. In the following, we will take a closer look into how the secure tunneling in the Nabto IoT platform differs from these.
What is device streaming, and why is it relevant?
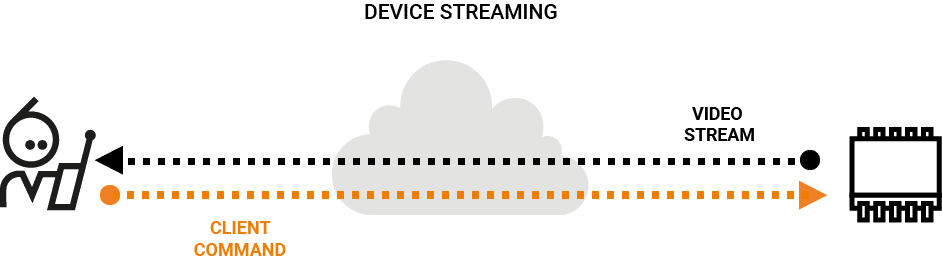
Device streaming is used when you collect or send data between a client, like an app on your smartphone, and an Internet of Things (IoT) device, like a surveillance camera, smart alarm, thermostat, etc. – anything that is connected to the internet. To do this, you can use different IoT solutions, like AWS, Azure or Nabto. The Nabto solution uses P2P technology, which has several advantages that the other solutions lack. Read along to figure out how.
User privacy and secure tunneling with end-to-end encryption
Secure tunneling to connected devices is the new hot topic, and the focus on privacy is important, now more than ever, when it comes to the field of the Internet of Things (IoT). IoT devices collect countless user data points and this makes the chance of hackability all the more worrying. Therefore, as the number of IoT devices increases, the more important it is to strengthen and improve the privacy of data within connected devices.
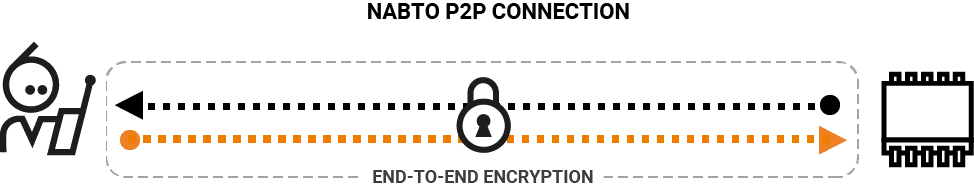
The type of connection to the IoT device has a huge impact on the level of user privacy. Both the AWS IoT Device Management and the Azure IoT Device Stream use relaying of data. The Nabto platform, on the other hand, uses a peer-to-peer (P2P) connection between the end-user client and the IoT device, where data is transmitted directly with an end-to-end encryption. Using tunnelling like AWS or Azure is less private as data relayed between peers must be passed in cleartext (ie, not encrypted) through the relay.

P2P results in better performance and a simpler solution
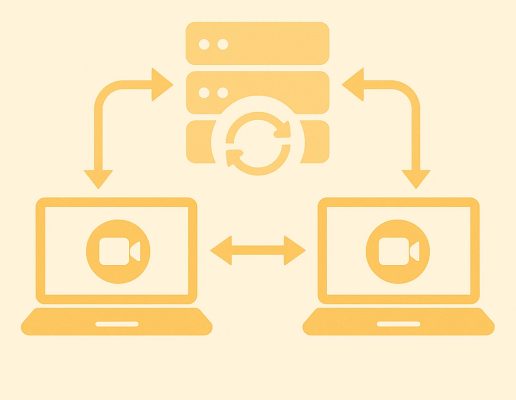
Besides the high level of privacy, the P2P connection also has a much lower latency than the solutions Amazon and Microsoft (among others) provide. With a direct P2P connection, where data only travels directly from client to IoT device and back, the latency is very low – whereas for a relay solution, the data travels from client to cloud server to IoT device. Data is hence encrypted, decrypted and then encrypted again – which combined with the longer network path makes the latency appreciably higher in the pure relay solution.
The challenges of a P2P connection are to locate the IP address of the device, and that firewalls are blocking access. The P2P solution allows for a much simpler architecture than other solutions, where the client can pair directly with the device, exchanging key public information without the need for central configuration. The Nabto platform uses the cloud to facilitate the connection between the two peers, which makes it possible to enter through firewalls and enable a direct connection. After the direct connection is enabled, the cloud is no longer needed as all data will be stored on the IoT device.
Nabto tunnels need much less resources on devices
Nabto tunnels are deployed in many very low ressource scenarios where a full HTTPS+TCP stack is not available: Nabto only needs a UDP stack and comes with just the necessary, optimized crypto implementations to provide secure tunnelling of TCP.